It’s been all over the news: ‘Ransomware’ cyber-attacks have been rampant this summer, especially for city governments. Today, the New York Times reported that 22 cities in Texas alone are “…simultaneously being held hostage for millions of dollars,” and there’s no end in sight. The attackers are requesting large sums of money in exchange for ‘decrypting’ the information that they maliciously encrypted – information that is virtually impossible to decrypt otherwise.
We came across our first ransomware attack in 2013. It wasn’t long after that we were getting dispatched weekly for attacks. There weren’t news articles or websites with advice on how to handle these situations yet – just posts from businesses and individuals enraged that their data could be so easily stolen and used against them.
What are Ransomware attacks?
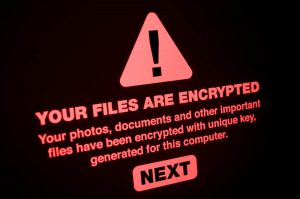
Ransomware attacks have 4 stages: Infect, Encrypt, Ransom, and Decrypt. Like many viruses, an attacker will send out emails, post links on social media from pages they’ve stolen, or attempt to infect websites with malicious code that can quickly install a small program on a computer. Unlike some infections that aim to steal financial information or redirect web searches to undesirable websites, ransomware infections run a script (program) on the target computer that encrypts the users information. Recent attacks have been more targeted with hackers gaining access to city networks or servers, then infecting large groups of connected computers.
Think of encryption like a cypher or secret code. If someone hands you a note that says ‘suriv,’ you wouldn’t know what it meant. If you were handed a second note, a ‘key’ that said ‘reverse’, you could easily determine that the reverse of ‘suriv’ is ‘virus’. Ransomware performs similar encryption on the users files, but instead of the key being as simple as ‘reverse’, it’s a 256-bit key, so tricks from The Da Vinci Code aren’t going to cut it.
Once data has been encrypted, it is impossible to access. Word documents won’t open, pictures won’t preview, spreadsheets, databases…etc. What can be accessed are the hundreds or thousands of plain text instructions that were added during the encryption, prompting the user to get in touch with the hacker and pay a ransom to have their data restored.
Once the ransom is paid, the instructions say, the hacker will send a second script that will decrypt the files, making them accessible and life ‘normal’ again, sans the plain text decryption instructions still littered throughout the filesystem. While there have been a number of successful ransomware decryptions, there have also been payouts with no decryption or failed decryption.
How To Prevent Ransomware Attacks
So far, only Windows operating systems have been largely affected by ransomware. Mac users can breathe a cautious sigh of relief (for now).
- Update, update, update
Windows and anti-virus updates are crucial for defending your computer or network from cyberattacks. Like the flu, these viruses change over time to elude the most recent preventative patches. Keeping your machine updated is one of the most important steps in preventing the latest attack method.
If your office has a managed IT plan with MCCS, your machines are automatically updated with the latest ransomware patches.
- Be careful where you click!
Unless your business was directly targeted by hackers (which is unlikely), the only way for the virus to get in is via a user’s actions. Double check email senders, be careful of suspicious links, and don’t fall for scams! There is definitely not a Nigerian Prince that needs your help transferring millions of dollars out of his country.
- ‘3 – 2 – 1’ Backup!
Even if all recommendations are followed, sometimes the attacker still gets in. Unless you’re willing to try your luck on a $75k ransom, automated backup systems are your saving grace.
3-2-1 is the standard for data protection. It means your data is always in 3 locations: 2 locally (on your computer and an external backup drive, for quick recovery) and 1 cloud backup.
It is extremely important that backups are incremental so that restored files are from a date prior to the infection, and isolated so the attack can’t infect the backup itself.
If your office has a managed IT plan with MCCS, your server and it’s data are protected by a 3-2-1 policy. If users save a lot of information on their local computers, you should consider 3-2-1 policies for your workstations as well.
- Cyber Security Insurance
If your business deals with a lot of sensitive information or would incur substantial losses from data or time loss, insurance is something you should consider.
What To Do When Under Attack

If your computer is acting up or seems to be working harder than normal, run a virus scan just to be safe. If you are having trouble opening files or see menacing messages popping up, shut down your computer immediately. The encryption process takes time – it’s not uncommon for many files to be recoverable if the process is stopped short. Once your system is off, call MCCS. These viruses spread over networks quickly so it’s imperative that infected computers are quarantined and healthy computers are isolated.
MCCS has helped nearly a dozen companies overcome ransomware attacks over the last 6 years. The latest surge in attacks indicates that more attacks are on the way. Be mindful while using your technology, make sure you are following the 3-2-1 backup policy, and immediately shut down any computers you suspect are infected. Hopefully you will never have to deal with an attack like this, but if you do, we’re here to help you get back to business.





